Update SQL Server 2022 to version 16.0.4120.1
What patches are you missing?
CVE Vulnerabilities for SQL Server 2022
| CVE | Published | Severity | Details | Exploitability | Impact | Vector |
| CVE‑2024‑0056 | 2024‑01‑09 18:15:47 | HIGH (9) | Microsoft.Data.SqlClient and System.Data.SqlClient SQL Data Provider Security Feature Bypass Vulnerability | 2 | 6 | NETWORK |
| CVE‑2023‑38169 | 2023‑08‑08 18:15:22 | HIGH (9) | Microsoft SQL OLE DB Remote Code Execution Vulnerability | 3 | 6 | NETWORK |
| CVE‑2023‑36785 | 2023‑10‑10 18:15:18 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑36730 | 2023‑10‑10 18:15:17 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑36728 | 2023‑10‑10 18:15:17 | MEDIUM (6) | Microsoft SQL Server Denial of Service Vulnerability | 2 | 4 | LOCAL |
| CVE‑2023‑36420 | 2023‑10‑10 18:15:12 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑36417 | 2023‑10‑10 18:15:12 | HIGH (8) | Microsoft SQL OLE DB Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑32028 | 2023‑06‑16 01:15:28 | HIGH (8) | Microsoft SQL OLE DB Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑32027 | 2023‑06‑16 01:15:28 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑32026 | 2023‑06‑16 01:15:28 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑32025 | 2023‑06‑16 01:15:28 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑29356 | 2023‑06‑16 01:15:28 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑29349 | 2023‑06‑16 01:15:28 | HIGH (8) | Microsoft ODBC and OLE DB Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑23384 | 2023‑04‑11 21:15:18 | HIGH (7) | Microsoft SQL Server Remote Code Execution Vulnerability | 4 | 3 | NETWORK |
| CVE‑2023‑21718 | 2023‑02‑14 20:15:15 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑21713 | 2023‑02‑14 20:15:14 | HIGH (9) | Microsoft SQL Server Remote Code Execution Vulnerability | 3 | 6 | NETWORK |
| CVE‑2023‑21705 | 2023‑02‑14 20:15:14 | HIGH (9) | Microsoft SQL Server Remote Code Execution Vulnerability | 3 | 6 | NETWORK |
| CVE‑2023‑21704 | 2023‑02‑14 20:15:14 | HIGH (8) | Microsoft ODBC Driver for SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2023‑21528 | 2023‑02‑14 20:15:12 | HIGH (8) | Microsoft SQL Server Remote Code Execution Vulnerability | 2 | 6 | LOCAL |
| CVE‑2022‑29143 | 2022‑06‑15 22:15:13 | HIGH (8) | Microsoft SQL Server Remote Code Execution Vulnerability | 2 | 6 | NETWORK |
| CVE‑2021‑1636 | 2021‑01‑12 20:15:30 | HIGH (9) | Microsoft SQL Elevation of Privilege Vulnerability | 3 | 6 | NETWORK |
| CVE‑2020‑0618 | 2020‑02‑11 22:15:13 | HIGH (9) | A remote code execution vulnerability exists in Microsoft SQL Server Reporting Services when it incorrectly handles page requests, aka 'Microsoft SQL Server Reporting Services Remote Code Execution Vulnerability'. | 3 | 6 | NETWORK |
| CVE‑2019‑1068 | 2019‑07‑15 19:15:17 | MEDIUM (7) | A remote code execution vulnerability exists in Microsoft SQL Server when it incorrectly handles processing of internal functions, aka 'Microsoft SQL Server Remote Code Execution Vulnerability'. | 0 | 0 | NETWORK |
| CVE‑2019‑0819 | 2019‑05‑16 19:29:01 | MEDIUM (4) | An information disclosure vulnerability exists in Microsoft SQL Server Analysis Services when it improperly enforces metadata permissions, aka 'Microsoft SQL Server Analysis Services Information Disclosure Vulnerability'. | 0 | 0 | NETWORK |
| CVE‑2018‑8273 | 2018‑08‑15 17:29:03 | CRITICAL (10) | A buffer overflow vulnerability exists in the Microsoft SQL Server that could allow remote code execution on an affected system, aka "Microsoft SQL Server Remote Code Execution Vulnerability." This affects Microsoft SQL Server. | 4 | 6 | NETWORK |
| CVE‑2017‑8516 | 2017‑08‑08 21:29:01 | HIGH (8) | Microsoft SQL Server Analysis Services in Microsoft SQL Server 2012, Microsoft SQL Server 2014, and Microsoft SQL Server 2016 allows an information disclosure vulnerability when it improperly enforces permissions, aka "Microsoft SQL Server Analysis Services Information Disclosure Vulnerability". | 4 | 4 | NETWORK |
| CVE‑2016‑7254 | 2016‑11‑10 07:00:08 | MEDIUM (7) | Microsoft SQL Server 2012 SP2 and 2012 SP3 does not properly perform a cast of an unspecified pointer, which allows remote authenticated users to gain privileges via unknown vectors, aka "SQL RDBMS Engine Elevation of Privilege Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2016‑7253 | 2016‑11‑10 07:00:07 | MEDIUM (7) | The agent in Microsoft SQL Server 2012 SP2, 2012 SP3, 2014 SP1, 2014 SP2, and 2016 does not properly check the atxcore.dll ACL, which allows remote authenticated users to gain privileges via unspecified vectors, aka "SQL Server Agent Elevation of Privilege Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2016‑7252 | 2016‑11‑10 07:00:06 | MEDIUM (4) | Microsoft SQL Server 2016 mishandles the FILESTREAM path, which allows remote authenticated users to gain privileges via unspecified vectors, aka "SQL Analysis Services Information Disclosure Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2016‑7251 | 2016‑11‑10 07:00:05 | MEDIUM (4) | Cross-site scripting (XSS) vulnerability in the MDS API in Microsoft SQL Server 2016 allows remote attackers to inject arbitrary web script or HTML via an unspecified parameter, aka "MDS API XSS Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2016‑7250 | 2016‑11‑10 07:00:04 | MEDIUM (7) | Microsoft SQL Server 2014 SP1, 2014 SP2, and 2016 does not properly perform a cast of an unspecified pointer, which allows remote authenticated users to gain privileges via unknown vectors, aka "SQL RDBMS Engine Elevation of Privilege Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2016‑7249 | 2016‑11‑10 07:00:03 | MEDIUM (7) | Microsoft SQL Server 2016 does not properly perform a cast of an unspecified pointer, which allows remote authenticated users to gain privileges via unknown vectors, aka "SQL RDBMS Engine Elevation of Privilege Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2015‑1763 | 2015‑07‑14 23:59:02 | HIGH (9) | Microsoft SQL Server 2008 SP3 and SP4, 2008 R2 SP2 and SP3, 2012 SP1 and SP2, and 2014 does not prevent use of uninitialized memory in certain attempts to execute virtual functions, which allows remote authenticated users to execute arbitrary code via a crafted query, aka "SQL Server Remote Code Execution Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2015‑1762 | 2015‑07‑14 23:59:01 | HIGH (7) | Microsoft SQL Server 2008 SP3 and SP4, 2008 R2 SP2 and SP3, 2012 SP1 and SP2, and 2014, when transactional replication is configured, does not prevent use of uninitialized memory in unspecified function calls, which allows remote authenticated users to execute arbitrary code by leveraging certain permissions and making a crafted query, as demonstrated by the VIEW SERVER STATE permission, aka "SQL Server Remote Code Execution Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2015‑1761 | 2015‑07‑14 23:59:00 | MEDIUM (7) | Microsoft SQL Server 2008 SP3 and SP4, 2008 R2 SP2 and SP3, 2012 SP1 and SP2, and 2014 uses an incorrect class during casts of unspecified pointers, which allows remote authenticated users to gain privileges by leveraging certain write access, aka "SQL Server Elevation of Privilege Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2014‑4061 | 2014‑08‑12 21:55:08 | MEDIUM (7) | Microsoft SQL Server 2008 SP3, 2008 R2 SP2, and 2012 SP1 does not properly control use of stack memory for processing of T-SQL batch commands, which allows remote authenticated users to cause a denial of service (daemon hang) via a crafted T-SQL statement, aka "Microsoft SQL Server Stack Overrun Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2014‑1820 | 2014‑08‑12 21:55:07 | MEDIUM (4) | Cross-site scripting (XSS) vulnerability in Master Data Services (MDS) in Microsoft SQL Server 2012 SP1 and 2014 on 64-bit platforms allows remote attackers to inject arbitrary web script or HTML via a crafted URL, aka "SQL Master Data Services XSS Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2012‑2552 | 2012‑10‑09 21:55:03 | MEDIUM (4) | Cross-site scripting (XSS) vulnerability in the SQL Server Report Manager in Microsoft SQL Server 2000 Reporting Services SP2 and SQL Server 2005 SP4, 2008 SP2 and SP3, 2008 R2 SP1, and 2012 allows remote attackers to inject arbitrary web script or HTML via an unspecified parameter, aka "Reflected XSS Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2012‑1856 | 2012‑08‑15 01:55:01 | HIGH (9) | The TabStrip ActiveX control in the Common Controls in MSCOMCTL.OCX in Microsoft Office 2003 SP3, Office 2003 Web Components SP3, Office 2007 SP2 and SP3, Office 2010 SP1, SQL Server 2000 SP4, SQL Server 2005 SP4, SQL Server 2008 SP2, SP3, R2, R2 SP1, and R2 SP2, Commerce Server 2002 SP4, Commerce Server 2007 SP2, Commerce Server 2009 Gold and R2, Host Integration Server 2004 SP1, Visual FoxPro 8.0 SP1, Visual FoxPro 9.0 SP2, and Visual Basic 6.0 Runtime allows remote attackers to execute arbitrary code via a crafted (1) document or (2) web page that triggers system-state corruption, aka "MSCOMCTL.OCX RCE Vulnerability." | 3 | 6 | NETWORK |
| CVE‑2012‑0158 | 2012‑04‑10 21:55:02 | HIGH (9) | The (1) ListView, (2) ListView2, (3) TreeView, and (4) TreeView2 ActiveX controls in MSCOMCTL.OCX in the Common Controls in Microsoft Office 2003 SP3, 2007 SP2 and SP3, and 2010 Gold and SP1; Office 2003 Web Components SP3; SQL Server 2000 SP4, 2005 SP4, and 2008 SP2, SP3, and R2; BizTalk Server 2002 SP1; Commerce Server 2002 SP4, 2007 SP2, and 2009 Gold and R2; Visual FoxPro 8.0 SP1 and 9.0 SP2; and Visual Basic 6.0 Runtime allow remote attackers to execute arbitrary code via a crafted (a) web site, (b) Office document, or (c) .rtf file that triggers "system state" corruption, as exploited in the wild in April 2012, aka "MSCOMCTL.OCX RCE Vulnerability." | 0 | 0 | NETWORK |
| CVE‑2011‑1280 | 2011‑06‑16 20:55:02 | MEDIUM (4) | The XML Editor in Microsoft InfoPath 2007 SP2 and 2010; SQL Server 2005 SP3 and SP4 and 2008 SP1, SP2, and R2; SQL Server Management Studio Express (SSMSE) 2005; and Visual Studio 2005 SP1, 2008 SP1, and 2010 does not properly handle external entities, which allows remote attackers to read arbitrary files via a crafted .disco (Web Service Discovery) file, aka "XML External Entities Resolution Vulnerability." | 0 | 0 | NETWORK |
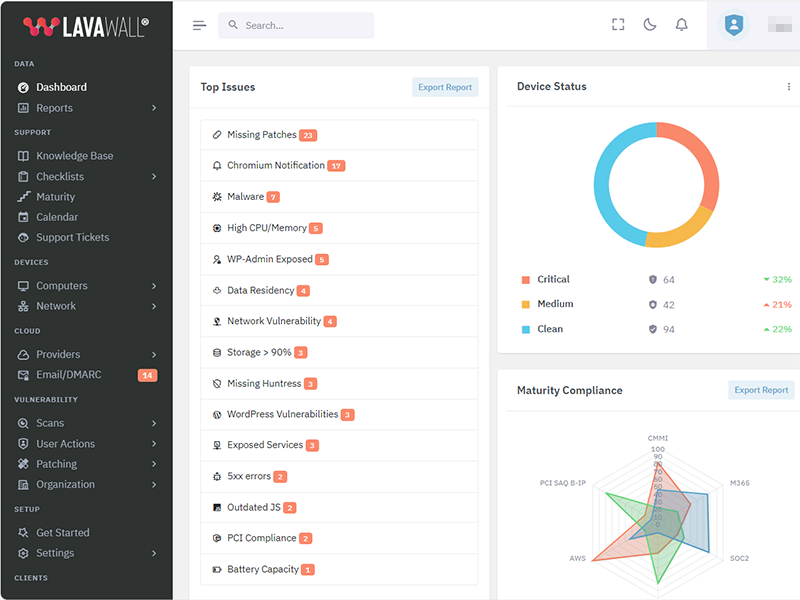
Get the IT stuff done that nobody wants to do.
Patch more applications, achieve compliance, and prevent problems while reducing stress with Lavawall®.
Security First
A security tool by security auditors. From Passkeys and Argon2i to source validation and MVSP principles, Lavawall® has you covered.
Constant Improvement
More features and more security added nearly every day.
More patchable programs added every week
While Ninite and other patching tools have had the same patch offerings for decades, we're monitoring stats to keep adding the most useful programs (currently over 7,438)!
Details matter
From wrapping TLS communications in extra encryption and uninstalling remote support tools when they aren't used to detailed statistical analysis of system and network performance, Lavawall® goes in-depth.
System Reliability
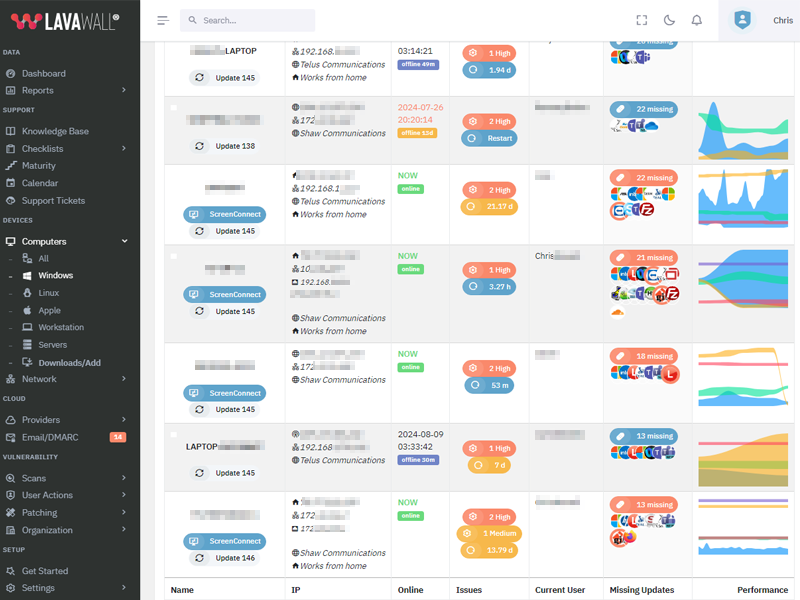
Monitor battery, disk, and process health. Lavawall® combines system health, age, operating system support, memory levels, and other attributes to prioritize systems for replacement.
Human and automated support
Get immediate fixes, user notifications, admin notifications -- and even security-certified human level 3 support when our advanced statistical analysis confirms a problem or anomaly.
| 2025‑03‑27 | 0.12.64.251 | Add efficiency to package management system |
| 2025‑03‑10 | 0.12.60.247 | |
| 2025‑03‑04 | 0.12.58.245 | |
| 2025‑03‑03 | 0.12.57.244 | Add TPM complience check and ensure consistent memory gathering in windows/linux/mac |
| 2025‑02‑28 | 0.12.56.243 | Windows RAM reporting and persistent scalability framework enhancements |
| 2025‑02‑27 | 0.12.55.242 | Battery health refinements |
| 2025‑02‑26 | 0.12.54.241 | Add battery health statistics |
| 2025‑02‑26 | 0.12.53.240 | |
| 2025‑01‑29 | 0.12.35.222 | Risk score refinements |
| 2025‑01‑17 | 0.12.29.216 | Enhanced compliance and non-standard AV |
| 2025‑01‑13 | 0.12.28.215 | Improved process graphs |
| 2025‑01‑07 | 0.12.27.214 | Antivirus details, compliance |
| 2024‑12‑27 | 0.12.24.211 | |
| 2024‑12‑02 | 0.12.19.206 | |
| 2024‑11‑22 | 0.12.18.205 | |
| 2024‑10‑30 | 0.12.8.195 | Mac update refinements |
| 2024‑10‑25 | 0.12.3.190 | |
| 2024‑10‑21 | 0.12.0.187 | Macos implementaiton, linux and windows improvements |
| 2024‑10‑16 | 0.11.128.186 | Linux stats and system information improvements, improvements for application shutdown |
| 2024‑09‑12 | 0.11.113.171 | CPU Optimizations and Packages reliability improvements |
| 2024‑09‑05 | 0.11.106.164 | Phased deployment enhancements |
| 2024‑09‑04 | 0.11.103.161 | |
| 2024‑09‑02 | 0.11.102.160 | CPU Optimizations and Packages reliability improvements |
| 2024‑08‑30 | 0.11.99.157 | CPU Optimizations and Packages reliability improvements |
| 2024‑08‑29 | 0.11.98.156 | CPU utilization and console event optimization |
| 2024‑08‑28 | 0.11.97.155 | Reliability to detect unusual updates like redistributables. |
| 2024‑08‑27 | 0.11.96.154 | |
| 2024‑08‑26 | 0.11.95.153 | Faster response for reboot requests |
| 2024‑08‑20 | 0.11.92.150 | Additional package upgrade pre-requisites |
| 2024‑08‑15 | 0.11.89.147 | |
| 2024‑08‑06 | 0.11.87.145 | |
| 2024‑07‑26 | 0.11.83.141 | Add resiliency for MAC duplicates and uptime |
| 2024‑07‑25 | 0.11.82.140 | Changes to facilitate cross-platform use. Bitlocker and Windows key refinements |
| 2024‑07‑15 | 0.11.80.138 | Antivirus and temperature added to configuration checks |
| 2024‑07‑15 | 0.11.79.137 | Add configuration checks for execution policy and secure boot |
| 2024‑07‑11 | 0.11.77.135 | load balancing refinements |
| 2024‑07‑10 | 0.11.76.134 | Add additional load balancing and data residency capabilities, add randomness to recurring task timings to decrease server load |
| 2024‑07‑05 | 0.11.74.132 | changes to graph and residual work on user imporsonation |
| 2024‑07‑04 | 0.11.73.131 | Add configuration checks for execution policy and secure boot. |
| 2024‑07‑03 | 0.11.72.130 | Enhanced event log monitoring |
| 2024‑07‑02 | 0.11.71.129 | Add details to Windows updates, enhanced risk metrics for application patches |
| 2024‑06‑19 | 0.11.65.123 | Update resiliancy and garbage collection |
| 2024‑06‑13 | 0.11.60.118 | Enhanced logging |
| 2024‑06‑12 | 0.11.55.113 | Include the primary drive serial number; MAC addresses for built-in wireless, Bluetooth, and ethernet into the device hash to restore uninstalled and reinstalled devices in cases where the motherboard serial is not unique |
| 2024‑06‑07 | 0.11.54.112 | Patch and package uninstall data addition |
| 2024‑06‑05 | 0.11.47.105 | refine per-user registry application listing |
| 2024‑06‑02 | 0.11.45.103 | uninstall and reinstall refinements, refine local logging, refine self-update and uninstall timing |
| 2024‑05‑30 | 0.11.21.79 | various bug fixes and improvements |
| 2024‑05‑28 | 0.11.16.74 | Error logging, registration, and uninstall improvements. |
| 2024‑05‑24 | 0.11.14.72 | applied changes for devices and login commands, changes for registration as well |
NOTE: changes after June 2024 are incorportated into the Windows Changelog as the codebases for Windows, Linux, and Mac were combined
| 2024‑05‑20 | 253 | Added cleanup of old .json files during a re-install |
| 2024‑05‑13 | 252 | Added apt-get update to install |
| 2024‑05‑06 | 248 | Allow restart to use /var/run/reboot-required if needrestart is not installed |
| 2024‑04‑22 | 239 | Improve internal update and version tracking |
| 2024‑04‑15 | 235 | Add support for Yum packages |
| 2024‑04‑08 | 233 | Align patching with Windows patch reporting |
| 2024‑04‑02 | 228 | Add support for needrestart |
| 2024‑03‑04 | 224 | Schedule restarts |
| 2024‑03‑25 | 221 | Add support for apt packages |
| 2024‑03‑18 | 212 | Implement release management |
| 2024‑03‑11 | 202 | Add user login monitoring |
| 2024‑03‑04 | 189 | Enhance installation reliability |
| 2024‑02‑26 | 187 | Exapand triggers to identify if the instance needs to be restarted |
| 2024‑02‑19 | 146 | Improve compatibility for non-AWS instances |
| 2024‑02‑14 | 138 | Add self-uninstall capabilities |
| 2024‑02‑12 | 135 | Enhance scheduling flexibility |
| 2024‑02‑07 | 132 | Add kernel version tracking |
| 2024‑02‑05 | 124 | Add device hash to cryptographic self-update script validation |
| 2024‑01‑29 | 107 | Enhance encryption of patch data |
| 2024‑01‑22 | 98 | Improve how available storage is calculated |
| 2024‑01‑15 | 97 | Move initial tasks from installation file to sub scripts |
| 2024‑05‑21 | 91 | Improve multi-distribution compatibility |
| 2024‑05‑21 | 79 | Improve encryption reliability |
| 2023‑12‑11 | 68 | Enhance cryptographic validation of new scripts before updating |
| 2023‑11‑20 | 62 | Add inner layer of AES encryption in case TLS inspection doesn't allow for a secure connection |
| 2023‑11‑27 | 56 | Additional base cases for resiliancy |
| 2023‑11‑20 | 54 | Additional headers added to authentication process during installation. |
| 2023‑11‑20 | 53 | Enhanced key management |
| 2023‑11‑15 | 51 | Add insecure installation parameter to allow installation in environments with TLS inspection or other machine-in-the-middle situations. |
| 2023‑11‑06 | 42 | Enhance redundant encryption during installation. |
| 2023‑10‑30 | 33 | Improve install-over compatibility |
| 2023‑10‑23 | 18 | Add reboot configuration and scheduling |
| 2023‑10‑23 | 17 | Add self-updating functionality. |
| 2023‑10‑16 | 15 | Add Linux patching information for apt |
| 2023‑10‑09 | 14 | Collect system information |
| 2023‑10‑09 | 13 | Add Linux distribution information |
| 2023‑09‑30 | 12 | Add memory monitoring |
| 2023‑09‑30 | 10 | Add hardware information |
| 2023‑09‑23 | 9 | Add AWS information |
| 2023‑09‑23 | 8 | Add customized schedule capability for configuration updates |
| 2023‑09‑23 | 7 | Add support for package monitoring using package and dpkg logs |
| 2023‑09‑16 | 6 | Add storage data configuration gathering |
| 2023‑09‑16 | 5 | Add CPU information |
Lavawall® was built from the ground up with these concerns and the Minimum Viable Secure Product requirements in mind.
Some of the controls we implemented include:
- PassKeys as the preferred primary authentication at no additional cost
- Single Sign-on using modern, maintained, and industry-standard protocols for all customers at no additional cost
- Multi-Factor Authentication as a non-negotiable default
- Encrypting communications the same way as TLS again within the TLS tunnel, so we can allow TLS inspection without breaking like Huntress or disclosing security vulnerabilities to eavesdroppers.
- Encouraging external vulnerability reports and customer testing
- Passwords checked against popular disclosed passwords, hashed before they leave your computer, and then stored using Argon2id
- Not requiring the use of passwords at all. We consider them a temporary backup authentication in case you can't use passkeys or SSO.
Lavawall® databases and front-end systems are hosted with AWS in Montréal, Québec, Canada.
We send emails through AWS in Ireland and dedicated servers in Calgary, Alberta, Canada.
We send text messages for additional identity verification through Twilio in the United States.
We store executables and pass requests through Cloudflare at your nearest edge location.
We use Cloudflare for risk management, turnstile, and web application firewall services.
We use LeadPages for landing pages.
We use Google and Facebook for analytics on our public-facing pages, but they do not have access to the console.
We integrate with third-party tools, such as Microsoft, Google, Huntress, Screen Connect, Axcient, and Datto in their respective locations. However, you must initiate these integrations through single sign-on or by enabling them in your Lavawall® console.
Active security by design
Lavawall® is under active development with the latest release including:
7,438+
Monitored Applications
61+
System Metrics
Actively manage your IT with Lavawall®
Patching
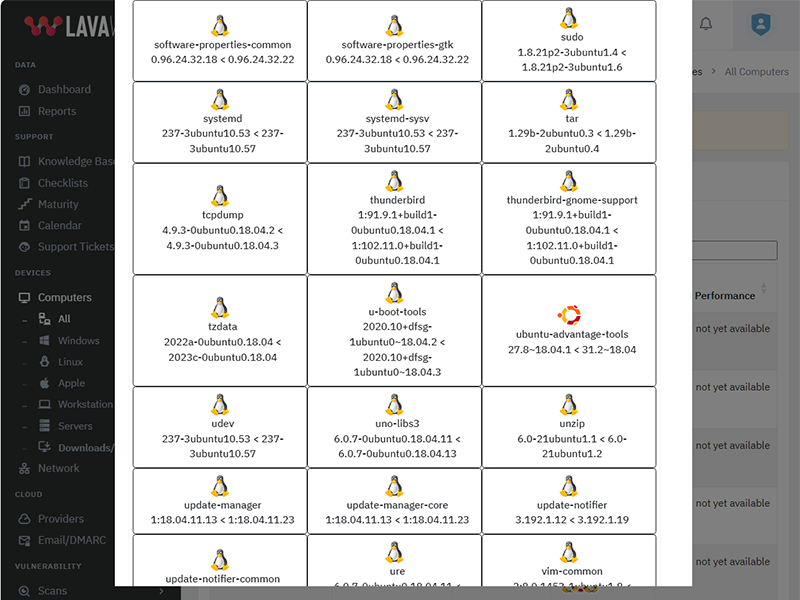
Updates Beyond Windows
Lavawall® prevents the 80% of breaches and failed audits due to missing patches and updates.
You can reduce application patching delays from 67 days to nearly immediate with the 7,438+ applications that Lavawall® monitors and patches.
Patch release monitoring
Monitor everything without having to select packages or “managed applications”
Patch impact classification
Standard and optional Windows patches
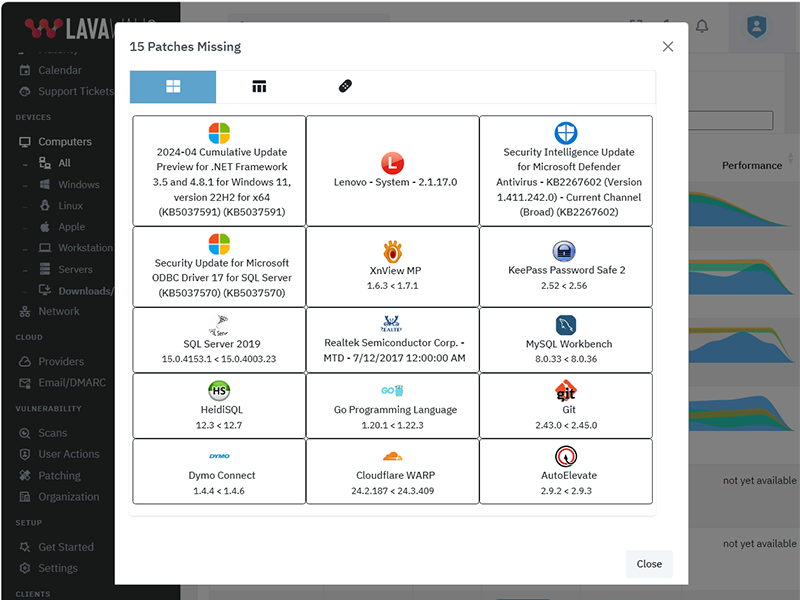
Application Patching
Some of the applications that Lavawall® monitors and audits include:
Logos are property of their respective trademark holders and are not affiliated with ThreeShield or Lavawall. We have not audited the security of most of the listed tools.
The above listing includes products that Lavawall® monitors through public information and/or proprietary statistical analysis.
Although we do have a partner relationship with some of the listed products and companies, they do not necessarily endorse Lavawall® or have integrations with our systems.
Learn More
Flexible Term; Flexible Service
Flexibility for your dynamic business
You need to get your arms around compliance and security and don't want to get locked into “high watermark” monthly invoices or multi-year contracts.
Pay-as-you-need monthly pricing
DIY, full management, and coaching options
Choose the plan that's right for you
Simple pricing. No hidden fees. Advanced features for you business.
Month
Annual
Get 2 months free with Annual!
Minimal
Pay-as-you go. No Commitments.
C$3.25 /computer/Month
C$32.50 /computer/Year
-
1 computer
or 1 of the following cloud integrations:
AWS, Axcient, Datto, Google, Huntress, M365, Sophos Central integrations
(each integration counts as 1 computer) -
50+ application patches
-
30-day Logs
-
Security configuration monitoring
-
Lavawall® support
-
Domain Scanning: C$20/domainDomain Scanning: C$200/domain
-
Level 3+ IT support for IT
-
IT coaching sessions
-
Automatic discount and upgrade to Business Standard at 77 devices
Business Standard
Basic services with 90-day logs
C$250 /Month
C$2,250 /Year
-
150 computers
Additional computers: C$2.50/computerAdditional computers: C$25/computer -
25 domains
Additional domains: C$15/domainAdditional domains: C$150/domain -
AWS, Axcient, Datto, Google, Huntress, M365, Sophos Central integrations
-
7,438+ application patch monitoring
-
90-day Logs
-
Security configuration monitoring
-
Lavawall® support
-
Level 3+ IT support for IT
-
IT coaching sessions
-
Automatic discount and upgrade to Full Service at 950 devices
Full Service
Optimize & audit-ready your IT
$2,250 /Month
$22,500 /Year
-
1,500 computers included
Additional computers: C$2/computerAdditional computers: C$20/computer -
125 domains included
Additional domains: C$10/domainAdditional domains: C$100/domain -
AWS, Axcient, Datto, Google, Huntress, M365, Sophos Central integrations
-
7,438+ application patch monitoring
-
365-day Logs
-
Security configuration monitoring
-
Lavawall® support
-
L3 IT support for IT
-
IT coaching sessions
Frequently Asked Questions
If you can not find answer to your question in our FAQ, you can always contact us or email us. We will answer you shortly!
General Questions
- Two years after a missing Plex Media Server led to the LastPass breach, the
Remote Monitorign and Management (RMM) tools availabel for Manged IT Service Providers (MSPs)
still didn't monitor for it.
Going through industry-specific applications, we noticed many were missing from the big RMM and patching providers. MSPs, insurance providers, and organizations that put their cleints at risk need to know about these risks, which lead to the largest number of critical audit findings and breaches - After 20 years of writing the same audit findings about system configurations, Payment Card Industry (PCI) compliance, and missing patches, our technical co-founder wanted to make it easier fo avoid these findings
- The existing risk visibility tools for insurance underwriters took a shallow look at Internet-facing risks. They -- along with all businesses -- need a deeper view of the threats that could actually lead to breaches.
- Domain risks
- Operating System (OS) patches
- Application patches
- Network vulnerabilities
- Cloud vulnerabilities
- OS configurations
You can use your own logo for the console and notifications. You can also use a CNAME to automatically brand your console.
Note: you cannot currently re-proxy the CNAME to Lavawall® through Cloudflare.
Lavawall® supports the following operating systems:
Lavawall® does not currently support non systemd distributions, such as Devuan, Artix Linux, PCLinuxOS, OpenWRT, and DD-WRT. However, we will support them by the end of 2024.
In June 2024, we combined the Windows and Linux systems for a consistent experience. This added support for RedHat and MacOS.
Privacy & Security
However, we do allow passwords and use passwords as part of the zero-knowledge encryption for your clients' sensitive data, such as Bitlocker keys and Personally-Identifiable Information (PII).
These passwords use Argon2id slow hashes with individual salts and peppers. They go through a few hash rounds on your computer before being sent to our servers for further hashing.
We have added an additional secure tunnel that mimics the TLS process within the public TLS tunnel. This extra tunnel provides authentication and privacy for the workstations and the Lavawall® servers to prevent attacks such as the one that took down Solar Winds.
Remote access is not enabled for read-only and audit situations.
Get In Touch
Have a quick question and don't want to talk? Send us a quick note with the form below and we'll reply within one business day.
NW Calgary:
ThreeShield Information Security Corporation
600 Crowfoot Crescent N.W., Suite 340
Calgary, Alberta
T3G 0B4
SE Calgary:
ThreeShield Information Security Corporation
105, 11500 - 29th St. SE
Calgary, Alberta
T2Z 3W9
Canada