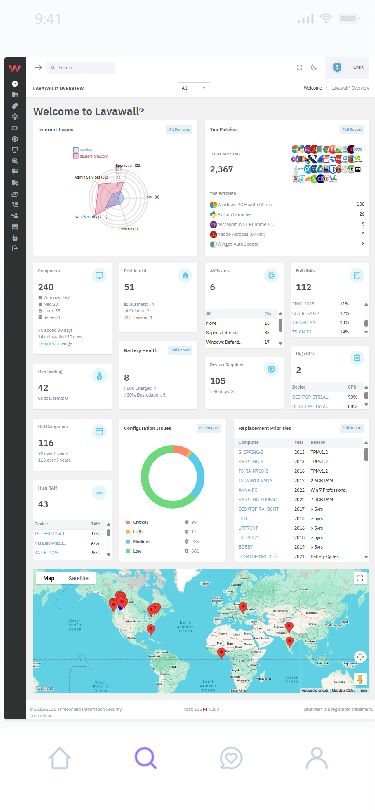
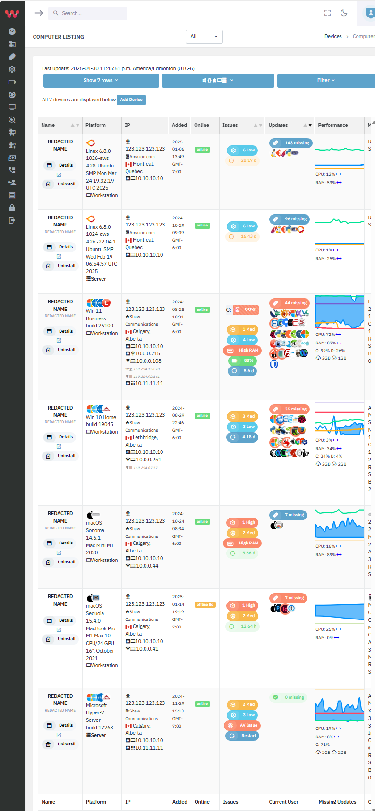
MSPs and lean IT teams lost control with outdated RMMs that miss issues that cost clients, and increase labour & insurance costs.
Regain Control
Lavawall gives full, intelligent, prioritized control back to you from computer reliability to cloud and rogue agentic AI.
It even gives you a sigh of relief when clients ask you if you meet CIS, CMMC, NIST, PCI, NERC, CPA, and Canadian privacy requirements.
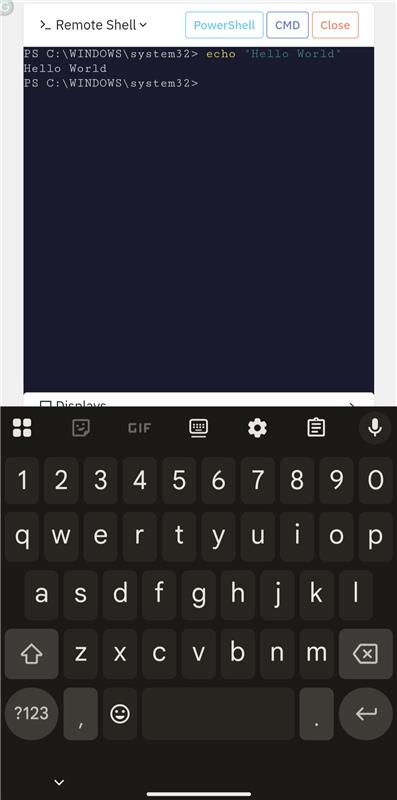
Most MSPs focus on antivirus and firefighting vulnerabilities. Lavawall® differentiates your stack and focuses on holistic hygiene so you can relax and stand out and fill a gap that justifies premium pricing while enabling hero-level secure remote support without requiring your laptop.
In addition to cross-platform patching, Lavawall® replaces expensive SEIMs with smart logging and notifications that cover your endpoints and cloud while amping up Microsoft 365, Entra, and Azure monitoring with intelligent breach detection and endpoint correlation that Entra ID, Defender, and SaaS alerting systems miss.
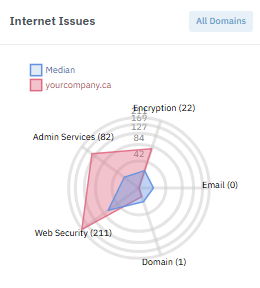
Internet
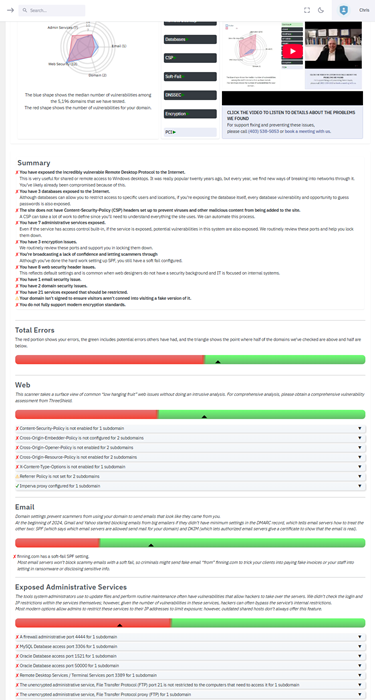
From transferrable domains and DMARC to outdated encryption and exposed admin tools on forgotten subdomains, Lavawall® even checks admin access to popular Content Management Systems, databases, and more!
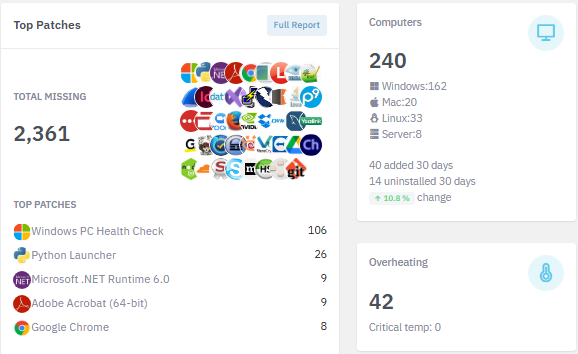
7,500+ Applications
Reduce downtime and support tickets by proactively addressing 7,533+ risk-ranked Windows, Mac, and Linux applications plus Windows, Mac, and Linux OS & firmware updates.
View applications
Find your vulnerabilities
Quiet Revelation
Lavawall® Internet and domain scans are so quiet, you don’t have to change firewall or WAF rules or worry about noisy alerts.
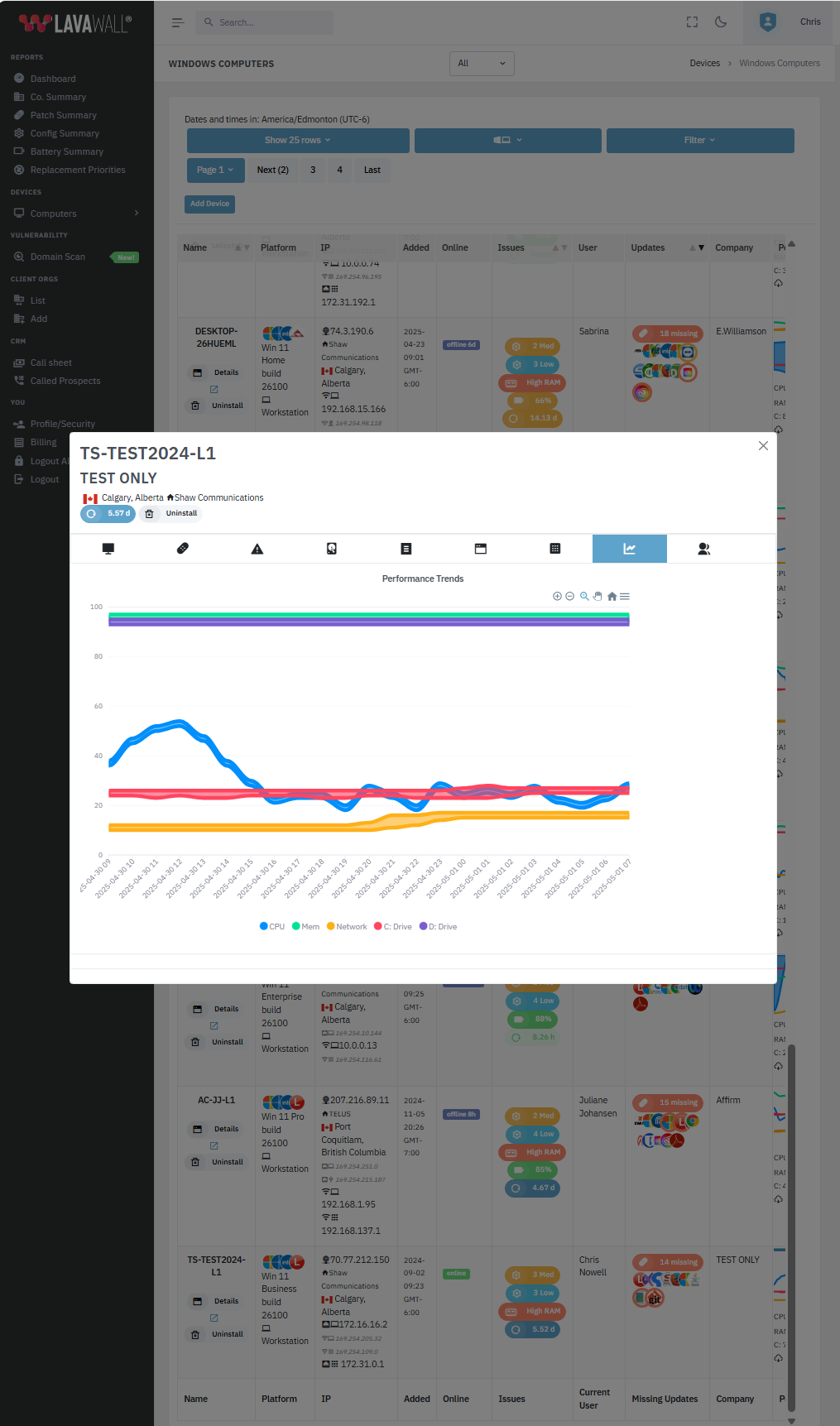
Amp up reliability with battery, temp, and other often-missed issues.
Fast LAN scans quickly find internal vulnerabilities, monitor for outages, and even printers running low on toner!
Easy Monitoring
From Huntress incidents, AV/MDR/XDR/EDR issues, Microsoft 365, Azure, and Entra breach and configuration detection, and domain/server issues to memory leaks.
Get a quick view of problems before they blow up into critical incidents -- and then enable easy, ongoing monitoring.
Seriously: negative-cost cybersecurity
Save money and make money
Client discovery & optimization
- Build accurate, profitable quotes with fast, comprehensive client discovery.
- Keep your clients by securing applications and settings that your competitors miss and even deliver beautiful automated reports in seconds that show the breaches they let in!
- Reduce costs and increase productivity by finding problems with batteries, disks, and applications before users complain.
We don’t do long-term contracts, but we do decrease your costs as you grow, so your costs are optimized and you don't have to worry if a client shrinks. We'll never send you a new bill based on a bogus “high water mark” from months ago.
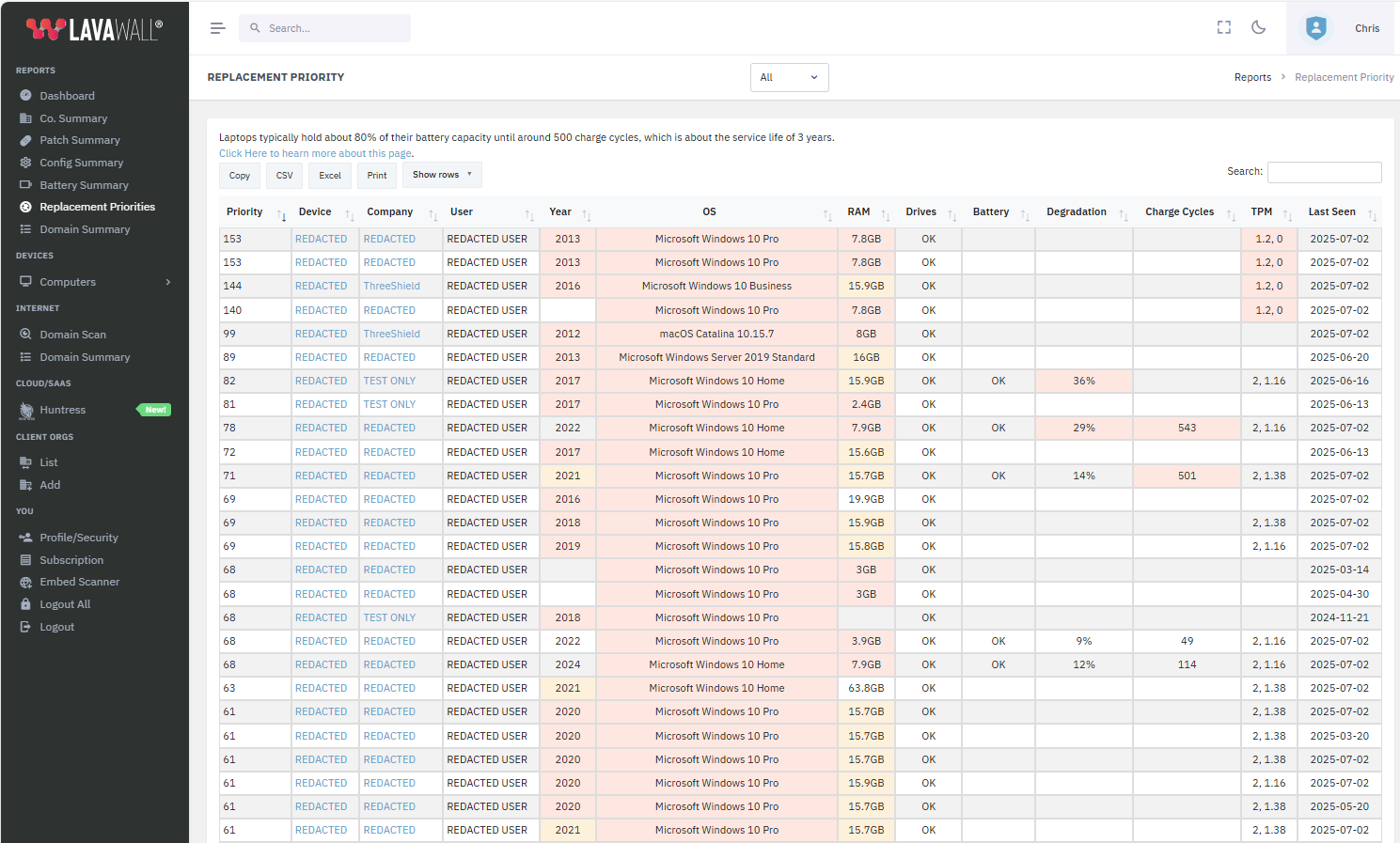
Client relationships with smart computer refresh
Deliver proactive upgrade recommendations that clients will actually act on.
Lavawall® helps you plan based with insights like degraded batteries, unreliable storage, maxed memory, or outdated TPM chips.
Increase reliability, justified sales, and satisfaction with optimized purchases driven by Lavawall’s simple, prioritized refresh lists.
Cyber insurance & Compliance
Save yourself and your clients 10-20% on cyber insurance by finding Internet-exposed issues before your insurance assessor's scan does.
Easily comply with CIS, CSF, PCI, CMMC, SOC2, HIA, PIPEDA, NERC CIP, CPA, Canadian Program for Cyber Security Certification (CPCSC), and other requirements with the Lavawall® GRC compliance system, which automates most of your compliance tasks.
White Label Security
Embed Lavawall® domain scanner results and printing functionality into your own website with custom phone and web call to actions to prove the need for cybersecurity to your MSP clients without requiring any admin access.
You can even use the tool to train your employees in cybersecurity and give about 87% of the value of a seasoned cybersecurity auditor.
Do you have questions?
Lavawall® is all about giving your users reliable computers, preventing hackers from getting in, and giving you confidence in arcane cybersecurity.
Here are the answers to some of the most common questions we hear.
If you have other questions, check out our FAQ page or call us in Calgary, Alberta at 1-403-538-5053; Vancouver, BC at 1-778-731-1339; or Mississauga, Ontario at 1-289-728-8829.
Seriously.
We were amazed that it worked too, but it is the easiest Mac security tool we’ve ever used.
We’re building more automated fix-it tools into Lavawall®, so it’s possible that if you ask us to help you, we might be able to give you early access to fix the problem yourself with one click.
If you’re working with one of our Managed IT Service Provider (MSP) partners, then we’ll direct you to them.
If you’re an MSP, we’ll happily help you directly or support your clients with our white label service.
If you aren't working with one of our partners, then we’ll gladly support you and quickly fix any issues that Lavawall® identifies.
We understand that this is a bit complicated. However, Lavawall® grew out of our MSP practice, where we endured vendors going around us to serve our clients directly so they could make a couple bucks and we don’t ever want to do that to our partners.
Take Lavawall® for a Spin
What would you like to do first? You can try either or both without a credit card.
If you decide to join, you can pay month-to-month without worries.